Raymond Cheng, Founder and CEO of Decrypt, named as one of Forbes’ Best In-State CPA for 2026
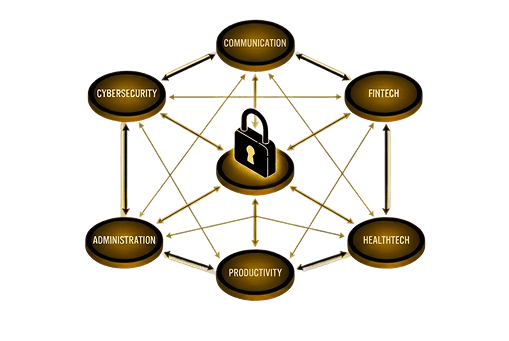
For B2B SaaS companies, compliance isn’t optional. Enterprise buyers require it. Investors expect it. And the longer it takes, the more deals sit in limbo.
Decrypt works with you through every step – educating your team, adapting to your processes, and signing the report your customers actually need. No readiness consultants. No handoffs. Just one firm that takes you from kickoff to certified.

How we do it
Client and compliance team jointly identify gaps in the existing security program, define risk priorities, and map improvement targets before any controls work begins.
Client implements all required security controls and finalises supporting documentation prior to the official start of the Attestation Period.
Client consistently operates all defined controls throughout the full Attestation Period, building the evidence trail auditors will review.
Compliance auditors actively test each control during the Attestation Period, verifying operating effectiveness through evidence review and walkthroughs.
Compliance team reviews all testing results, resolves any exceptions, and drafts the formal certification report for client review and sign-off.
Compliance team issues the final signed security certification report — completing the full audit lifecycle and confirming your compliance status.

Decrypt is independent. No PE ownership, no corporate parent, no pressure to scale at the expense of your audit. You work with a firm that answers to its clients.


America’s Best-In-State CPAs for 2025 & 2026

CPA.CITP, CISSP, CISA, CCSK, CIPP/E, ISO 27001 Lead Auditor, ISO 42001 Lead Auditor

Our Reviews

Co-Founder Brick Towers AG

CEO, Tillion.ai

CEO, Leen Inc

CEO · jumbomail.me

Mid-Market

Small Business

Small Business · France
Our Latest Articles






Type I is a point-in-time report confirming your security controls are designed correctly. Type II covers an observation period - typically 6 to 12 months - and confirms that those controls are actually working. Most enterprise buyers require Type II before signing a contract.
Vanta and Drata are software tools that help you collect and organize evidence. They don't perform audits or issue reports. Decrypt is a licensed CPA firm - we conduct the audit, sign the report, and issue the certification your customers are asking for. If you're already using Vanta or Drata, we work alongside them.
A Type I audit typically takes 4 to 6 weeks. A Type II audit requires a minimum 6-month observation period, though the active audit work is much shorter. Our clients get certified 50% faster on average - we keep the process moving so your deals don't sit in limbo.
Yes. Many clients pursue SOC 2 alongside ISO 27001 or other frameworks. Because the same team handles every engagement, evidence collected for one audit can often carry over to others - cutting duplicate work and time.
It's more common than you'd think. The biggest complaints we hear are auditor turnover, lack of communication, and junior staff who don't understand SaaS products. We work differently - same team every engagement, senior-level auditors, and clear communication throughout.
It depends on the scope and complexity of your environment. What we can tell you upfront is that we use fixed-fee pricing - no hourly billing, no surprise invoices mid-engagement. Book a discovery call today.
Get Started
Tell us about your company and we’ll get back to you with a clear path to certification – including timeline and pricing.
decrypt.cpa uses cookies for site functionality, usage analytics, and marketing attribution. Manage your preferences below — your choice applies across the site and you can change it any time. See our Cookie Policy for details.