|
Article Summary
|
Trust is no longer assumed. It is verified.
If your organization handles customer data, your clients expect clear, verifiable proof that your systems and processes meet recognized security standards. SOC 2 has emerged as one of the most widely accepted frameworks for demonstrating this assurance.
For startups and growing organizations, this requirement directly influences customer acquisition, partnership opportunities, and market credibility.
However, achieving SOC 2 compliance is not simply an audit exercise. Many organizations face delays because they enter the audit phase without fully understanding their control environment, risk posture, or documentation readiness. Missing policies, incomplete evidence, and unclear audit scope often result in remediation cycles that extend certification timelines and increase operational costs.
This is why a SOC 2 readiness assessment is a critical first step.
A SOC 2 readiness assessment allows you to evaluate your existing controls, identify gaps, and align your systems and processes with the SOC 2 Trust Services Criteria before the formal audit begins.
For small and mid-sized organizations, particularly those pursuing SOC 2 for the first time or preparing for renewal, a readiness assessment ensures your efforts remain focused, efficient, and aligned with audit expectations.
This blog provides a comprehensive SOC 2 readiness assessment checklist to help you understand what to evaluate, what to implement, and how to prepare your organization for efficient, and successful compliance.
What Is a SOC 2 Readiness Assessment and Why It Matters for Your Compliance Journey
A SOC 2 readiness assessment is a structured pre-audit evaluation of your organization’s controls, policies, systems, and documentation. It measures how well your current environment aligns with the SOC 2 Trust Services Criteria (TSC), which define the standards for managing and protecting customer data.
In practice, it serves as a formal gap analysis. It helps you determine whether your controls are properly designed, implemented, and supported by evidence. More importantly, it shows you exactly what needs to be fixed before you engage an auditor. This step helps you move forward with confidence instead of entering an audit unprepared.
What Does a SOC 2 Readiness Assessment Evaluate?
A SOC 2 readiness assessment evaluates whether your organization’s controls are properly designed, implemented, and capable of operating effectively in alignment with the SOC 2 Trust Services Criteria. It assesses the full scope of people, processes, and technology that auditors will review during a SOC 2 examination.
Key areas of evaluation include:
- Control design and implementation effectiveness
- Whether controls are appropriately designed to meet SOC 2 requirements and are consistently implemented across systems and processes.
- Security policies and governance framework
- The existence of formal, approved policies and a governance structure that defines roles, responsibilities, and oversight.
- Access control and user lifecycle management
- How user access is provisioned, reviewed, and revoked, including enforcement of least privilege and authentication controls.
- Risk management processes
- How risks are identified, assessed, documented, and mitigated across the organization.
- Change management and system operations
- Whether changes to systems are tested, approved, and tracked to prevent unauthorized or risky modifications.
- Monitoring, logging, and alerting
- The ability to detect, log, and respond to security events and anomalies in a timely manner.
- Incident response and issue management
- Whether security incidents are properly identified, documented, escalated, and resolved according to defined procedures.
- Vendor and third-party risk management
- How third-party providers are evaluated, monitored, and controlled to mitigate external risks.
- Evidence availability and audit trail readiness
- Whether sufficient, reliable evidence exists to demonstrate that controls are operating effectively over time (especially important for SOC 2 Type II).
- Alignment with SOC 2 Trust Services Criteria
- The extent to which controls map to and satisfy applicable criteria such as Security, Availability, and Confidentiality.
Why a SOC 2 Readiness Assessment Is Essential for Your Organization
If you are planning to pursue SOC 2 compliance, your readiness assessment is one of the most important steps in the process. It ensures you are fully prepared before entering the audit phase.
Without this step, you risk delays, audit failures, and unnecessary operational disruption. A SOC 2 readiness assessment gives you clarity, control, and a structured path to certification.
- Prevent Audit Failures and Costly Delays
If you enter a SOC 2 audit without proper preparation, you increase the risk of audit findings and remediation requirements. This can delay your certification by several months.
A readiness assessment helps you identify gaps in your controls, policies, and documentation before the audit begins. You can fix these issues early, reducing remediation time and preventing repeated audit cycles. This preparation helps you complete your audit more efficient and avoids unexpected compliance setbacks.
- Clarify Your Audit Scope and Trust Services Criteria
You need to clearly define what falls within your SOC 2 audit scope. This includes your systems, infrastructure, applications, and processes that handle customer data.
The SOC 2 scope varies based on your business model, service offerings, and customer commitments. Without proper scope definition, you may include unnecessary systems or miss critical areas.
A readiness assessment helps you select the appropriate Trust Services Criteria and ensures your controls align with your actual operational environment. This allows you to focus only on what matters and avoid unnecessary complexity.
- Strengthen Your Internal Security and Operational Maturity
When you conduct a readiness assessment, you gain a clear view of your organization’s security and operational maturity. You understand how well your current controls protect your systems and data. This process improves your visibility into key areas such as:
- Access control and user permissions
- Risk identification and mitigation
- Incident response preparedness
- Security governance and accountability
You can strengthen weak areas and ensure your organization operates with consistent, well-defined security practices.
- Build Customer and Partner Trust
Your customers and partners expect you to protect their data. SOC 2 demonstrates that your organization follows recognized security and compliance standards.
A readiness assessment helps you achieve certification efficiently, which strengthens your credibility in the market. It shows that your organization takes security seriously and operates with discipline and accountability.
This is especially important if you are working with enterprise customers or expanding into regulated markets.
When Should You Conduct a SOC 2 Readiness Assessment?
You should conduct your readiness assessment well before your formal audit. This gives you enough time to identify gaps and implement corrective actions.
Recommended Timeline for Type I and Type II Audits
Your timeline depends on the type of SOC 2 audit you are pursuing. For a SOC 2 Type I audit, you should begin your readiness assessment at least 3 to 4 months before the audit. This ensures your controls are properly designed and documented.
For a SOC 2 Type II audit, you need to demonstrate that your controls operate effectively over a period of time, typically between 3 and 12 months. Your readiness assessment ensures your controls are functioning consistently before this observation period begins. Starting early helps you avoid delays and ensures a smoother audit process.
Signs Your Organization Is Ready for a SOC 2 Readiness Assessment
Your organization is ready for a SOC 2 readiness assessment when the foundational elements of your security and compliance program are defined, implemented, and operating consistently. At this stage, you should have sufficient maturity across people, processes, and technology to evaluate your controls against audit expectations.
Key indicators of readiness include:
- Clearly defined system boundaries and audit scope
- You have identified all in-scope systems, services, infrastructure, and processes, with a clear understanding of where customer data is stored, processed, and transmitted.
- Security controls are implemented and documented
- Core controls—such as access management, encryption, monitoring, and operational safeguards—are actively enforced and supported by formal, approved policies and procedures
- Access control and user lifecycle processes are in place
- User access is properly provisioned, reviewed, and revoked, with enforcement of least privilege, role-based access, and strong authentication mechanisms
- Risk assessment and risk management processes are established
- Risks have been formally identified, assessed, and documented, with mitigation strategies tracked and aligned to your control environment
- Change management processes are operational
- System changes are tested, approved, and documented, with controls in place to prevent unauthorized or untracked modifications
- Monitoring, logging, and alerting are functioning
- Systems generate logs and alerts that are actively reviewed, enabling timely detection and response to security events
- Incident response processes are defined and tested
- You have documented procedures for identifying, escalating, and resolving incidents, and your team understands how to execute them.
- Vendor and third-party risk management is established
- Third-party providers are evaluated, approved, and monitored, with appropriate controls over external dependencies
- You can consistently generate, retain, and organize evidence (e.g., logs, reports, tickets) that demonstrates controls are operating effectively over time
- Roles, responsibilities, and control ownership are clearly assigned
- Control owners are identified, accountable, and actively responsible for maintaining and monitoring their controls
- Governance and oversight mechanisms exist
- There is management oversight of the compliance program, including periodic reviews, approvals, and accountability structures
- Alignment with SOC 2 Trust Services Criteria has been established
- Your controls are mapped to the relevant Trust Services Criteria (e.g., Security, Availability, Confidentiality), ensuring full coverage of audit requirements
SOC 2 Readiness Assessment Checklist for Audit Preparation and Compliance Success
The following helps you efficiently achieve SOC 2 compliance audit by evaluating your current security posture, identifying gaps, and ensuring your organization is fully prepared before engaging an auditor.
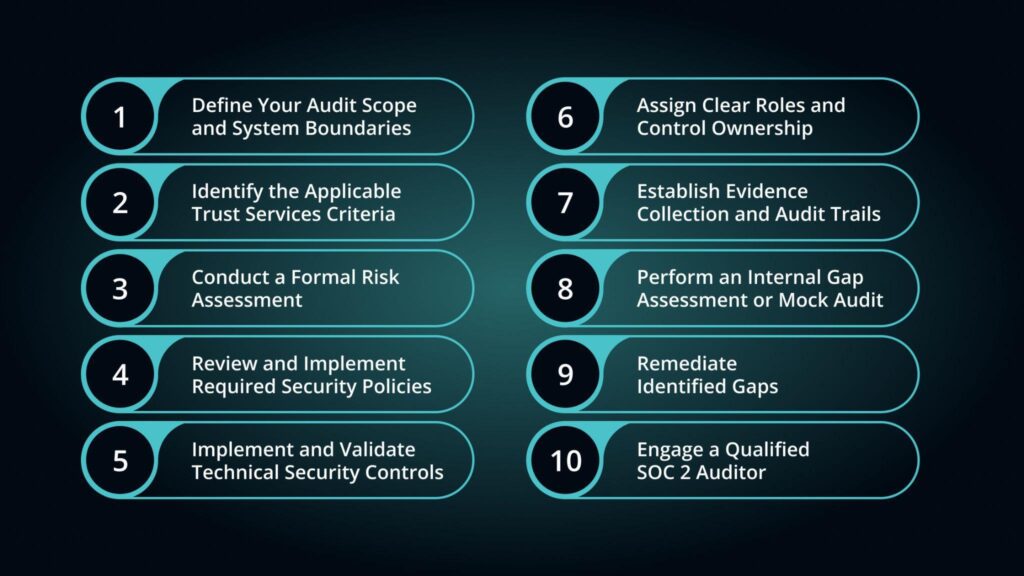
Step 1: Define Your Audit Scope and System Boundaries
You need to clearly identify what will be included in your SOC 2 audit. This ensures you focus only on relevant systems and avoid unnecessary complexity.
Start by identifying all systems, applications, and processes that handle customer data. This may include your cloud infrastructure, production environments, internal controls, and third-party integrations.
You should also document your system architecture, infrastructure components, and data flows. This gives you a clear understanding of how data moves through your environment and what needs to be secured.
Step 2: Identify the Applicable Trust Services Criteria
You must determine which SOC 2 Trust Services Criteria apply to your organization.
Security is mandatory for all SOC 2 audits. It ensures your systems are protected against unauthorized access and security threats. You may also need to include additional criteria based on your services and customer expectations:
- Availability, if your customers depend on system uptime
- Confidentiality, if you handle sensitive or proprietary data
- Processing Integrity, if you process customer transactions or data
- Privacy, if you collect or manage personal information
You should align your criteria selection with your contractual obligations, customer requirements, and regulatory environment.
Step 3: Conduct a Formal Risk Assessment
You need to identify and evaluate risks that could impact the security and reliability of your systems.
- Start by identifying internal risks such as unauthorized access, misconfigurations, or employee errors. You should also consider external risks such as cyberattacks, vendor vulnerabilities, or infrastructure failures.
- Next, assess the likelihood and impact of each risk. This helps you prioritize which risks require immediate attention.
- You must also document your mitigation strategies. This shows that your organization actively manages risks and takes preventive measures to protect customer data.
A structured risk assessment demonstrates operational maturity and prepares you for audit scrutiny.
Step 4: Review and Implement Required Security Policies
You must ensure your organization has formal, documented security policies that define how systems and data are protected. Key policies you need include:
- Access Control Policy to manage user access and permissions
- Information Security Policy to define your overall security framework
- Incident Response Policy to handle and respond to security incidents
- Vendor Management Policy to manage third-party risks
- Change Management Policy to control system changes and prevent unauthorized modifications
These policies must be documented, approved, and communicated to your team. They provide the governance framework auditors expect to see.
Step 5: Implement and Validate Technical Security Controls
You need to ensure your technical controls are properly implemented and actively protect your systems. This includes implementing identity and access management controls to restrict system access based on roles and responsibilities.
You should also implement encryption to protect sensitive data in transit and at rest. Logging and monitoring systems must be in place to detect suspicious activity and maintain audit trails. You also need vulnerability management processes to regularly identify and fix security weaknesses.
Backup and disaster recovery controls must ensure that your data can be restored in the event of system failure or data loss. These controls form the technical foundation of your SOC 2 compliance.
Step 6: Assign Clear Roles and Control Ownership
You must assign responsibility for each control to specific individuals or teams. This ensures accountability and proper control management. Your engineering, IT, HR, and leadership teams should each have defined roles in maintaining compliance.
You should clearly document who is responsible for implementing, monitoring, and maintaining each control. Clear ownership ensures controls remain active, effective, and audit-ready.
Step 7: Establish Evidence Collection and Audit Trails
You need to collect and maintain evidence that proves your controls are working effectively. This includes system logs, access records, training documentation, policy acknowledgments, and configuration records.
Your evidence should be organized, complete, and easily accessible. This ensures auditors can verify your compliance without delays or additional remediation requests.
Step 8: Perform an Internal Gap Assessment or Mock Audit
You should simulate audit conditions by conducting an internal gap assessment or mock audit.
This helps you evaluate whether your controls meet SOC 2 requirements.
You can identify missing documentation, incomplete controls, or weak processes before the formal audit begins. This step allows you to proactively address issues and enter the audit fully prepared.
Step 9: Remediate Identified Gaps
You must address any gaps identified during your readiness assessment. Start by prioritizing high-risk issues that could affect audit outcomes.
Implement remediation plans with clear timelines and assigned ownership. You should also document all remediation actions to demonstrate continuous improvement. Closing these gaps ensures your organization meets audit expectations.
Step 10: Engage a Qualified SOC 2 Auditor
Once your readiness assessment is complete and gaps are resolved, you can engage a licensed CPA firm to conduct your SOC 2 audit. Your readiness assessment ensures your controls, documentation, and evidence are audit-ready. This allows the audit process to proceed efficiently and increases your likelihood of successful certification.
Strengthen Your SOC 2 Readiness with Professional Guidance from Decrypt Compliance
SOC 2 compliance doesn’t have to slow down your business. Many companies face delays because they’re unsure where to start, what evidence to gather, or how to prepare for an audit without disrupting operations. Decrypt Compliance removes that uncertainty, providing clear guidance from day one and eliminating the guesswork that causes delays.
As a tech-first audit and compliance firm, we specialize in helping startups and growing teams achieve SOC 2 compliance quickly and accurately, with a deep understanding of how modern companies operate.
Decrypt Compliance keeps your certification journey smooth, efficient, and audit-ready.